Introduction
Since Russia’s full-scale invasion in February 2022, both Russia and Ukraine have at times disrupted and at other times preserved the internet – a collective institution based on shared infrastructure and protocols vital for information access and co-ordination. The observed fluctuations in how belligerents treat the internet challenge the common assumption that combatants are more likely to destroy than to deliberately safeguard mutual interdependence during war. While Russia carried out more than twenty documented internet outages in 2022 alone, it more often preserved internet access in order to exploit cyberspace for intelligence gathering and disinformation (AF Brantly and N Brantly Reference Brantly and Brantly2024).
This case highlights an increasingly urgent yet underexplored question in international relations (IR): How do combatants navigate interdependence during wartime? Much existing scholarship views interdependence and conflict as fundamentally incompatible, highlighting how shared institutions (for example, trade agreements, humanitarian aid routes, the internet) foster peace and how war disrupts institutional co-operation (Crescenzi Reference Crescenzi2003; North et al. Reference North, Wallis and Weingast2009; Oneal and Russett Reference Oneal and Russett2001). However, recent research suggests that the relationship between collective institutions and conflict is not always negative (Carnegie Reference Carnegie2021; Goddard Reference Goddard2018). Institutions may not only survive war but also be deliberately maintained or strategically manipulated in ways that support military aims. Building on this scholarship, we argue that institutions can become operational tools of warfare, selectively disrupted or preserved by combatants depending on the tactical demands and constraints they face on the battlefield.
We explain this variation by theorizing how different wartime strategies – maneuver, attrition, and punishment – shape the incentives and constraints combatants face in deciding whether to maintain or disrupt shared institutions. Specifically, we argue that battlefield dynamics influence the feasibility and desirability of institutional disruption. Attackers engaged in maneuver warfare are more likely to disrupt common institutions to gain surprise and disorient defenders. Defenders against such maneuver operations, by contrast, face greater constraints and are more reliant on institutional continuity for co-ordination. In attrition warfare, the relative stability of front lines encourages selective use of shared institutions by all combatants, while punishment campaigns in enemy-held areas pose unique challenges that often incentivize preserving connectivity.
We test our theory using the ongoing war in Ukraine – a conflict of immense geopolitical significance. Importantly, it presents a hard case for our theory due to potential data biases stemming from underreported cyber-operations and unintended disruptions during intense attrition warfare. Finding support for our theory in this scenario only strengthens its reliability.
This article makes several contributions. Theoretically, it challenges prevailing views, which tend to posit either a negative or positive relationship between collective institutions and warfare by focusing on that relationship at the onset and termination of a conflict. In contrast, we shift the focus to the fluctuating patterns of interdependence during wartime, showing how institutions are actively managed in response to shifting battlefield conditions. The Ukraine war provides rich temporal and geographic variation in battlefield dynamics, allowing us to develop a nuanced, locality-based measure of military strategy – advancing prior research that often assumes a single dominant strategy per war (Stam Reference Stam1998) or battle (Biddle Reference Biddle2004). By grounding our analysis in the conduct of war rather than its causes or outcomes, this study advances both the study of wartime strategy and broader IR debates on institutional resilience under conditions of armed conflict.
Methodologically, we advance empirical research on the microdynamics of conflict by introducing a new measure of battlefield strategy and a novel approach to capturing internet disruptions during war. Collaborating with computer science co-authors, we develop tools that detect geolocated, daily internet outages – moving beyond prior approaches focused on broad, prolonged national shutdowns. Drawing on quantitative analysis of these disruptions, as well as qualitative evidence from Ukraine and the 2020 and 2023 Armenia–Azerbaijan conflicts, we find robust support for our theoretical claims, demonstrating that the strategic targeting and management of internet connectivity is not unique to Ukraine but reflects a broader pattern across contemporary conflicts (Access Now 2021,2024).
Institutions and Conflict
Institutions are generally defined as the ‘rules of the game’ that structure human interactions (North Reference North1990; Ostrom Reference Ostrom1990). By establishing shared expectations and reducing uncertainty, institutions promote co-ordination and increase interdependence among actors (Morrow Reference Morrow2014). This interdependence has traditionally been seen as incompatible with war. Classic IR scholarship associates strong institutions with peace and conflict resolution, and it views war as a breakdown of co-operative order (Waltz Reference Waltz1979). Accordingly, much research has focused on how institutional strength reduces the likelihood of war (Oneal and Russett Reference Oneal and Russett2001) or how war undermines institutional durability.
However, recent scholarship has begun to complicate this binary. Scholars now show that institutional interdependence can be exploited during conflict rather than merely undermined. Institutions can serve as platforms for covert competition, intelligence collection, and strategic manipulation (Carnegie Reference Carnegie2021; Farrell and Newman Reference Farrell and Newman2019). Actors may weaponize institutional ties to shape asymmetric dependencies or project influence through seemingly co-operative mechanisms (Goddard and Nexon Reference Goddard and Nexon2016; Lindsay Reference Lindsay2025). These insights suggest that institutions may not only persist but actually play functional roles during conflict, especially when actors find strategic advantage in maintaining them.
Building on this work, our approach shifts the focus from whether institutions prevent or survive war to how they are actively used as tools during wartime operations. We develop a theory of institutional status that is grounded in the strategic demands of different military campaigns. While much of the literature treats the relationship between conflict and institutions as either structurally negative or positive, we emphasize that institutional interdependence is not static but varies across time and space in response to shifting battlefield conditions. That is, depending on an actor’s battlefield position and strategic constraints at a given moment, the actor may maintain institutions like the internet in order to use or exploit them – for communication, intelligence, or influence – or the actor may disrupt those institutions in order to deny those same advantages to an opponent.
By focusing on the microdynamics of warfighting – particularly how combatants manage interdependent institutions like the internet – we contribute to a growing body of research that moves beyond war onset and termination to examine the tactical logic of conflict behavior. In doing so, we show that institutional interdependence can be a flexible asset shaped by wartime strategy, with implications not only for how conflicts are fought but also for how peace is rebuilt – depending on whether and how institutions are preserved or damaged during war.
A Theory of Institutional Status in Wartime
Our theory of institutional status centers on two strategic options: actors can either maintain or disrupt collective institutions. We broadly define disruption as a deliberate decision by combatants to interrupt collective institutions during conflict. We contrast disruption with maintenance, the deliberate decision to preserve institutions. Among the many collective institutions that can operate during wartime – such as trade networks and humanitarian aid organizations – we have chosen to focus on the internet. This choice reflects both its empirical traceability and its theoretical value as a paradigmatic case of institutional interdependence under fire.
While commonly understood as infrastructure, the internet also functions as a collective institution because it is governed by shared rules, protocols, and technical standards that enable co-ordination and communication at scale. These non-material elements – such as the Transmission Control Protocol/Internet Protocol, Border Gateway Protocol, and Domain Name System – bind disparate systems together, making the internet a system of human-devised constraints that structure interaction. In this sense, the internet is a sociotechnical institution, blending material components (like fiber-optic cables and servers) with normative and rule-based components (like routing protocols and access policies).Footnote 1
An institutional interpretation of the internet (DeNardis Reference DeNardis2014) also diverges from the common view of cyberspace as a geographic ‘domain’ like air, sea, or outer space (Branch Reference Branch2021). In physical domains like airspace, denying access to a rival makes the domain easier to exploit. In contrast, restricting others’ internet access simultaneously limits one’s own; conversely, maintaining open access allows everyone to benefit.Footnote 2 This characteristic highlights a common feature of collective institutions: institutional disruption negates benefits for all parties while institutional maintenance preserves institutional benefits and opens avenues for exploitation to all.
This dual nature of institutional interdependence – offering both opportunity and vulnerability – raises a broader strategic question: How do combatants decide when to preserve or disrupt access to collective institutions in wartime? To answer this question, we first define these two options and then show how variation in operational constraints – shaped by time and space depending on the military strategy employed – influences these choices.
Institutional Disruption versus Institutional Maintenance
Strategic disruption of collective institutions in wartime can take many forms. For example, in German-occupied USSR, Soviet partisans sabotaged the railway network to disrupt German logistics and supply routes, though this also temporarily impeded the transport of Soviet troops and supplies. Where the institution’s primary utility is to enable communication, as with the internet, disruption becomes a strategy to incapacitate an enemy’s communication, thereby disrupting military command and control. The military logic is straightforward: a force unable to communicate is more vulnerable to defeat. This logic underpins disruptions to Ukraine’s digital infrastructure.
Yet combatants do not always choose disruption. Institutional maintenance can offer significant strategic advantages, particularly through exploitation – which we define broadly as subversion of a collective institution’s normal function to gain a competitive edge. In some conflicts, combatants have sought to exploit humanitarian develirty mechanisms to transport military supplies under the dover of aid–for example, during the Bosnian War, where weapons were allegedly smuggled through or alongside humanitarian convoys into desieged areas. In the internet context, exploitation often involves cyber-operations for intelligence gathering or dissemination of (dis)information.
This trade-off between disruption and maintenance reflects a core tension of institutional interdependence: shared systems enhance both capability and vulnerability. As shown in Table 1, disruption and maintenance strategies impose distinct costs and benefits, forcing combatants to weigh the military pros and cons of each.
Institutional disruption versus institutional maintenance

Institutional Status and Battlefield Constraints
Classic IR theory often treats war as an anarchic environment where institutions collapse (Waltz Reference Waltz1979). However, we argue that institutions can persist in war – not as relics of peacetime, but as actively contested tools, shaped by strategic incentives. This perspective builds on research that views institutionalization and anarchy as dynamic rather than binary conditions (Mcconaughey et al. Reference Mcconaughey, Musgrave and Nexon2018; Lake Reference Lake2009). In this sense, we also argue that war is not monolithic: constraints on combatants fluctuate over time and shape their decisions to either disrupt or maintain collective institutions.
Prior research identifies several sources of constraints – geography, logistics, audience costs (Carr and Tanczer Reference Carr and Tanczer2018), deterrence (Gannon et al. Reference Gannon, Gartzke, Lindsay and Schram2024), alliances, and peacekeeping operations (Lanoszka Reference Lanoszka2022) – but overlooks the influence of combat dynamics themselves. Wars are episodic, often alternating between fluid movements and static, sustained engagements. These shifts affect the degree of battlefield control a combatant enjoys – and, with it, their freedom of action. We focus on three core military strategies – maneuver, attrition, and punishment – each associated with distinct combat dynamics (Pape Reference Pape1996; Stam Reference Stam1998). Our central claim is that operational freedom drives institutional disruption, while constraint favors institutional maintenance.
While our theory models combatant organizations as unitary actors, we recognize that deviations from high command strategy can occur at the tactical level due to principal-agent problems. Nevertheless, modern military technologies – such as real-time communication, GPS co-ordination, and surveillance systems – can reduce information asymmetries and enhance command-and-control capacity, even in fluid battlefield environments. Moreover, contemporary doctrines often emphasize ‘mission command’, granting local autonomy within the bounds of a shared strategic intent. As a result, decentralized or autonomous actions frequently remain aligned with broader institutional goals. Our focus, therefore, remains on explaining aggregate patterns in targeting behavior rather than assuming perfect hierarchical control.
Maneuver strategy: high offensive freedom and disruption incentives
Maneuver warfare is a military strategy that emphasizes speed, mobility, and flexibility to gain operational advantage by disrupting the enemy’s decision making. It focuses on exploiting weaknesses in the opponent’s disposition while maintaining control over one’s own forces and freedom of action.
Even though mobility is a typical feature of both offensive and defensive combatants in maneuver warfare, the two sides differ markedly in their levels of control and freedom – and, therefore, in their level of constraints – during maneuvers. Offensive combatants initiate maneuvers when they are least constrained by combat dynamics – that is, when they have greatest control over the battlefield, with the freedom to decide when and where to strike. Therefore, offensive maneuver warfare is proactive and aggressive, focusing on rapid, decisive movements to seize initiative and exploit enemy weaknesses. It prioritizes secrecy and surprise to break through defenses and sow destabilizing confusion within enemy ranks.
The dynamic nature of maneuver warfare makes institutional disruption attractive to offensive combatants for several reasons. When attempting to force openings and create chaos within enemy ranks, it makes sense for offensive combatants to disrupt collective institutions, such as communication networks or logistical systems, to create opportunities for surprise and significantly hinder the enemy’s ability to co-ordinate and respond effectively, thereby amplifying the offensive actor’s advantage. Additionally, communication disruption heightens confusion within enemy ranks and within the civilian population that supports them, increasing the psychological shock of maneuvers. Disruption operations are also often easier to plan than intelligence exploitation, as they focus on blocking communications rather than managing an ongoing intrusion. This simplicity is particularly valuable in the context of maneuver warfare, given the complexity of the combined-arms approach that often characterizes this strategy.
Unlike offensive conduct in maneuver warfare, which is proactive, defensive conduct in maneuver warfare is largely reactive, focused on responding to the initiatives of offensive forces by absorbing enemy attacks while maintaining flexibility for counterattacks. Defensive combatants use tactics like fortifying positions and delaying actions, with a primary goal of preserving the status quo. As a result, defensive combatants are most constrained during maneuver warfare, as it is the combat dynamic in which they have the least control over the battlefield. In this context, defensive forces are less likely than offensive forces to disrupt collective institutions during maneuver warfare for the following reasons.
First, maintenance of collective institutions can be crucial for sustaining defensive operations, managing resources, and co-ordinating responses. For example, the internet serves as a vital communication tool, enabling defenders to organize, share information, and maintain a degree of operational coherence despite pressure from offensive actions. While defenders might not have many opportunities to exploit shared institutions (for example, to use the internet for intelligence collection or influence operations), preserving them provides stability and resilience, enabling defenders to remain operational despite constant offensive threats.
Secondly, while disruption operations are often simpler to execute than institutional exploitation, they may nevertheless require more logistical effort than defensive combatants can afford to expend during fast-moving maneuver warfare, diverting precious resources and attention from more urgent counter-responses to offensive operations. Additionally, because far-less-constrained offensive combatants are more likely to target shared institutions when they initiate a maneuver, they may pre-emptively undermine defenders’ ability to do so.
This underscores the role of strategic interaction in shaping combatants’ decisions to disrupt institutions. Actors must consider not only their own operational constraints but also how their adversary might respond to, or pre-empt, such actions. Disruption is most attractive when combatants expect their efforts to catch the enemy off-guard or strike at a moment of heightened vulnerability. For offensive combatants, this moment often comes early in a maneuver campaign, when speed and surprise are paramount. For defensive combatants, however, maneuver warfare tends to be less conducive to disruption. Their primary focus is preserving control and countering enemy advances – tasks that demand co-ordination, logistical stability, and – often – the very institutional infrastructure that disruption would undermine.
HYPOTHESIS 1A (Offensive v. Defensive Maneuver): During maneuver warfare, offensive combatants are more/less likely than defensive combatants to disrupt/maintain institutions (internet connectivity).
Attrition strategy: mutual constraints, strategic maintenance
Attrition warfare occupies a middle ground between the extreme freedom of offensive maneuvers and extreme constraints of defensive maneuvers, imposing a relatively high degree of constraints on both sides. This relative equalizing of battlefield control makes it more difficult to distinguish between offensive and defensive operations in attrition warfare. We therefore do not make this distinction in our hypotheses regarding attrition warfare when comparing it to offensive and defensive maneuvering.Footnote 3
While maneuver warfare prioritizes mobility, attrition is marked by relative stasis, in that it is conducted by combatants entrenched along a well-defined geographical front, whose mutual goal is to gradually wear down the enemy’s strength and exhaust enemy resources through sustained attacks. In this sense, attrition is a relatively stable combat dynamic, even as it is also a costly one in terms of lives and resources. Over time, predictable patterns emerge: front lines become more defined and static, defenses strengthen, and supply lines are established to allow forces to regroup and resupply in safer rear areas. Unlike maneuver warfare, where tactical decision making is decentralized to allow frontline commanders to adapt quickly, attrition warfare often involves more centralized command and control, with logistics and civil infrastructure developing along the front. This predictability can make the tempo of battle so routine that the risks of war may be taken for granted by soldiers, politicians, and civilians, alike.
While the mutual constraints of attrition warfare limit combatants’ flexibility, its predictability enables sustained operations, making maintenance of collective institutions both more feasible and more desirable than disruption. In an attrition-based stalemate, where both sides seek ways to break the deadlock, stable institutions become crucial because they provide opportunities for exploitation. Specifically, combatants can leverage internet connectivity for cyber or influence operations. Maintaining normal connectivity can lull the enemy into a false sense of security, setting the stage for intelligence gathering via cyber-espionage operations to identify weaknesses, plan future offensives, and provide early warning of enemy attacks. Internet-based propaganda and disinformation that target civilian and military forces, or even international audiences, can undermine the enemy’s morale, weaken internal cohesion, and boost support for friendly forces.
At the same time, the value of functioning institutions in attrition warfare is mutual. For instance, both sides benefit from access to communication and information infrastructure, which is crucial for gathering intelligence that may enable a transition to maneuver operations. Thus, even though each side is aware that the other may exploit these institutions, the strategic benefits of preserving access often outweigh the risks. Rather than deny themselves access by disrupting institutions, combatants in attrition are often willing to accept some degree of vulnerability in exchange for continued exploitation. In this context, the cost of institutional disruption – cutting off one’s own access to valuable intelligence and operational co-ordination – can exceed the benefits of disrupting the enemy’s access.
This trade-off contrasts with conditions under maneuver warfare. Attrition warfare is more constrained than offensive maneuvering. The greater freedom offensive combatants have in maneuver warfare, we argue, encourages them to disrupt rather than exploit institutions, given the tactical advantage of maintaining mobility and surprise (Hypothesis 1B). In contrast, attrition warfare is less constrained than defensive maneuvering. Despite the stability of the front, combatants in attrition warfare can take more initiative in their actions than can defensive combatants in maneuver warfare, who are largely reactive. This relative freedom, we argue, explains why combatants in attrition warfare are more likely to disrupt collective institutions, such as internet connectivity, than are defensive combatants in maneuver warfare (Hypothesis 1C).
HYPOTHESIS 1B (Attrition v. Offensive Maneuver): Combatants are less/more likely to disrupt/maintain institutions (internet connectivity) when engaged in attrition combat than when conducting offensive maneuver campaigns.
HYPOTHESIS 1C (Attrition v. Defensive Maneuver): Combatants are more/less likely to disrupt/maintain institutions (internet connectivity) when engaged in attrition combat than when conducting defensive maneuver campaigns.
Punishment strategy: spatial constraints, institutional exploitation
Punishment strategy targets enemy civilians – typically through airstrikes, long-range attacks, or economic blockades. While punishment strategies are traditionally defined by their focus on coercing civilian populations (Pape Reference Pape1996), we emphasize the location where they take place. The fact that these operations are typically waged in enemy-held areas, away from active front lines, imposes constraints that shape the institutional choices available to combatants, making institutional exploitation both more attractive and more feasible than disruption.
When combatants lack direct control over terrain, as they do in enemy-controlled territories, they must rely on intelligence gathering, signaling, and indirect influence. In such environments, maintaining access to collective institutions like the internet becomes strategically useful. Rather than disrupting institutions, therefore, combatants conducting punishment campaigns are more likely to exploit them – for example, to monitor civilian sentiment, spread disinformation, or co-ordinate remote strikes.
In contrast, when combatants wage attacks on contested territories, they enjoy greater operational freedom. Here, disruption of shared institutions becomes more attractive, as it can degrade enemy co-ordination, create confusion, and amplify the advantages of initiative and surprise. In contrast, institutions located deeper in enemy-controlled territories may be supported by more heavily defended infrastructure, making successful disruption more difficult or costly and, as a result, reducing incentives for attackers to target them. It might also be the case that institutions in enemy-controlled areas are already integrated into the enemy’s command structure and thus less accessible to frontline combatants. In contrast, shared institutional infrastructure in contested zones often remains exposed and actively used by both sides, making it a more immediate and vulnerable target. Therefore, we argue that combatants are more likely to disrupt institutions such as internet connectivity in contested territories, where maneuvers and attrition take place, than in enemy-controlled areas, where punishment strategies do.
HYPOTHESIS 2 (Punishment): Combatants are more/less likely to disrupt/maintain institutions (internet connectivity) in contested territories – where maneuver warfare and attrition typically occur – than in territories under enemy control, where punishment strategies are more common.
Why We Focus on the War in Ukraine
To test our theory, we focus on the case of the 2022 Russian invasion of Ukraine for three primary reasons. First, as the largest land war since World War II, the case’s significance is immense. Secondly, the Ukraine war is a hard case for our theory due to potential attenuation biases in our data. Internet outages during the conflict could result from either cyber-operations or military actions. If they stem from cyber-operations, the resilience of Ukrainian internet infrastructure,Footnote 4 combined with Western support before and during this war (Kostyuk and Brantly Reference Kostyuk and Brantly2022), could bias our data towards underreporting Russian-sponsored cyber-operations aimed at causing outages. On the other hand, if internet outages result from military actions, the intensity of brute-force attrition warfare could cause more disruptions, even if the forces did not intend to target the internet. This would lead to an overrepresentation of actor-attributed outages during attrition warfare compared to offensive maneuver warfare. Finally, by employing cutting-edge techniques from the internet measurement community, we collect near-real-time, micro-level, geolocated data on regional internet outages. We discuss this unique data, which had not previously been utilized in IR research, in the section below (see Dependent Variable).
Research Design
Our temporal unit of analysis is a day. Our analysis starts on 24 February 2022 (Russia invades Ukraine) and ends on 31 December 2023, covering 676 days of war. Our spatial unit of analysis is a province (’oblast’), given that this is the smallest spatial unit of the Internet Outage Detection and Analysis (IODA) data. For the main analysis, we cover twenty-four oblasts and the capital city of Kyiv. In all, we have 16,900 oblast-day observations in our data.
Our analysis combines both quantitative and qualitative components. The quantitative analysis examines Russia’s use of internet outages during the war in Ukraine, as the number of such incidents allows for robust statistical testing. Although Ukraine also used internet outages to disrupt enemy communications, these occurrences were too few for meaningful quantitative analysis.Footnote 5 Given the scarcity of Ukraine-attributed outages, we rely on descriptive evidence and anecdotal evidence to demonstrate that Ukrainian actions align with our theoretical expectations (see Online Appendix Section 3). While we use the same data sources to identify our dependent and independent variables for both the Ukrainian and Russian sides, the remainder of the research design and findings section focuses on Russian actions.
Dependent Variable
Our dependent variable Rus Internet Outage is a dummy indicating whether the Russian state – represented by either the government or military – is responsible for disruptions in internet connectivity on a specific day in a given oblast.
To create this variable, we used the following three data sources. Members of our team have pioneered IODA methods, which employ cutting-edge internet measurement techniques to monitor digital traffic patterns and identify macroscopic internet outages (Internet Intelligence Lab 2022). IODA uses four different data sources that employ distinct and complementary methodologies for monitoring internet connectivity: Border Gateway Protocol announcements, active probing, network telescope data, and Google product traffic (available only at the country level). For this analysis, we focus mainly on IODA’s active probing signal, with availability tuned to the oblast level; this displays a more consistent pattern of normal connectivity compared to the sometimes-erratic telescope data and is best able to reflect power outages. Every 10 minutes, the IODA system adaptively probes approximately 3.5 M /24 network blocks worldwide. When /24 network blocks stop responding to IODA’s probes, this indicates possible disconnection from the internet.
To identify internet outages, we used a daily sum of drops in internet connectivity for each oblast using both a mean-shift change detection and standard deviation change detection. The mean-shift change detection algorithm identifies longer-duration drops in connectivity due to mean-shift changes in active probing. To identify mean-shift changes, we first divided the time series into fifteen segments, with one three-week segment and fourteen four-week segments. We applied mean-shift change point detection separately for each of the fifteen segments. The results of the mean-shift change were hand inspected to ensure detection of the most apparent mean-shift changes. We employ standard deviation change detection to identify shorter but sharp drops in active probing that may not cause a mean shift but do represent short-duration drops in connectivity. For every oblast, we first selected a week before Russia’s invasion as the reference standard deviation and identified all the time intervals when active probing values fall below four standard deviations from the mean of that segment. We used both the mean-shift change and standard deviation to capture a count of drops in connectivity per oblast.
Since IODA data indicates only whether outages occurred and does not detail the reasons behind them, we turned to a second source that identifies outages attributed to Moscow. Specifically, we utilized Access Now’s #KeepItOn Shutdown Tracker Optimization Project (STOP), which relies on various local and international news reports, personal accounts, and technical sourcesFootnote 6 to record and contextualize internet shutdowns (for example, Russian cyber-attacks on internet service providers; military operations targeting internet infrastructure; or soldiers dismantling telecommunication equipment). Since IODA is unable to geolocate satellite network signals, it does not capture the internet provided by Starlink. To make sure we capture such data, we complemented outages targeting Starlink already recorded in STOP with a few additional instances of such outages collected from public sources.
Main Explanatory Variable
Our main explanatory variable is a combatant’s level of constraints, which is related to the military strategy they employ. According to our theory, maneuver and attrition warfare occur in contested territories along the front line, whereas punishment warfare is conducted in opponent-controlled territories.
To determine which territories are contested and which are under opponent control, we use Zhukov (Reference Zhukov2023)’s Violent Incident Information from News Articles (VIINA) (v2.0) to create a factor variable for Territorial Control, which has three levels: ‘Russian occupation’, ‘Contested’, and ‘Ukrainian controlled’. A region is classified into one of these categories when at least 80 per cent of its territory falls under Russian control or Ukrainian control. Regions that do not meet either threshold are classified as contested.Footnote 7 Using this classification, we identify operations that take place in contested regions along the front line as maneuver or attrition warfare and operations in Ukrainian-controlled territories, where Russia lacks territorial control and faces greater operational constraints, as punishment.
Having differentiated between maneuver/attrition and punishment warfare based on location, we now turn to distinguishing between maneuver and attrition warfare, both of which occur in contested territories. To identify offensive and defensive maneuver warfare and attrition warfare, we relied on expert assessments provided by reputable research organizations and NGOs that have systematically tracked the progression of the conflict. Chief among these are the Center for Strategic and International Studies, the Institute for the Study of War, and other defense and security think tanks that have published widely cited operational timelines and analyses. These organizations employ military analysts and regional experts with backgrounds in defense policy, intelligence analysis, and conflict studies, which qualifies them as credible sources for categorizing phases of warfare. Table 1 in Online Appendix Section 1 provides samples of these sources.
Based on these external classifications, we categorize actions on the contested territories as follows: ‘Initial invasion’ (24 February 2022 to 7 April 2022) is classified as ‘Rus Offensive Maneuver’, the ‘Southeastern front’ (8 April 2022 to 28 August 2022), ‘Second stalemate’ (12 November 2022 to 7 June 2023), and ‘Winter campaigns’ (1 December 2023 to 31 December 2023) are categorized as ‘Attrition’ and ‘Ukrainian counteroffensive I’ (29 August 2022 to 11 December 22) and ‘Ukrainian counteroffensive II’ (8 June 23 to 30 November 2023) are classified as ‘Rus Defensive Maneuver’.Footnote 8
We also considered alternative ways to distinguish between maneuver and attrition warfare, such as tracking territorial gains, fatalities, or specific military tactics to capture finer, day-to-day battlefield dynamics. However, each of these measures has significant limitations. Territorial gains reflect successful maneuvers, which represent a small portion of overall maneuver efforts. Furthermore, there is no consensus on how much daily territorial change is needed to distinguish maneuver warfare from attrition warfare. Fatalities are similarly ambiguous – they occur in both maneuver and attrition contexts and often reflect force size or capabilities rather than strategy. Likewise, tactics like airstrikes can serve both offensive and defensive purposes (for example, in counteroffensive operations), further complicating classification. We discuss these limitations in more detail in Online Appendix Section 1, demonstrating that expert-coded military strategy remains the best measure given the data at hand.
While not without limitations, our approach advances prior work by incorporating both spatial and temporal dynamics, offering a more nuanced understanding of how warfare unfolds across time and space. This approach advances previous work that primarily focuses on a single dominant strategy used either throughout an entire war (Stam Reference Stam1998) or within a major battle (Biddle Reference Biddle2004).
Figure 1 shows the initiation dates of Russian-sponsored internet outages (white lines) across the different oblasts. Three patterns stand out. First, outages were more frequent during offensive maneuvers than during attrition, even though periods of maneuvering were much shorter. Second, attrition still saw more outages than defensive maneuvers. Third, Russia executed fewer outages for punishment in Ukrainian-controlled areas than for maneuvering and attrition along the front line.
Russian-sponsored internet outage initiation (white lines) by oblast during different war strategies in the Russo-Ukrainian conflict.

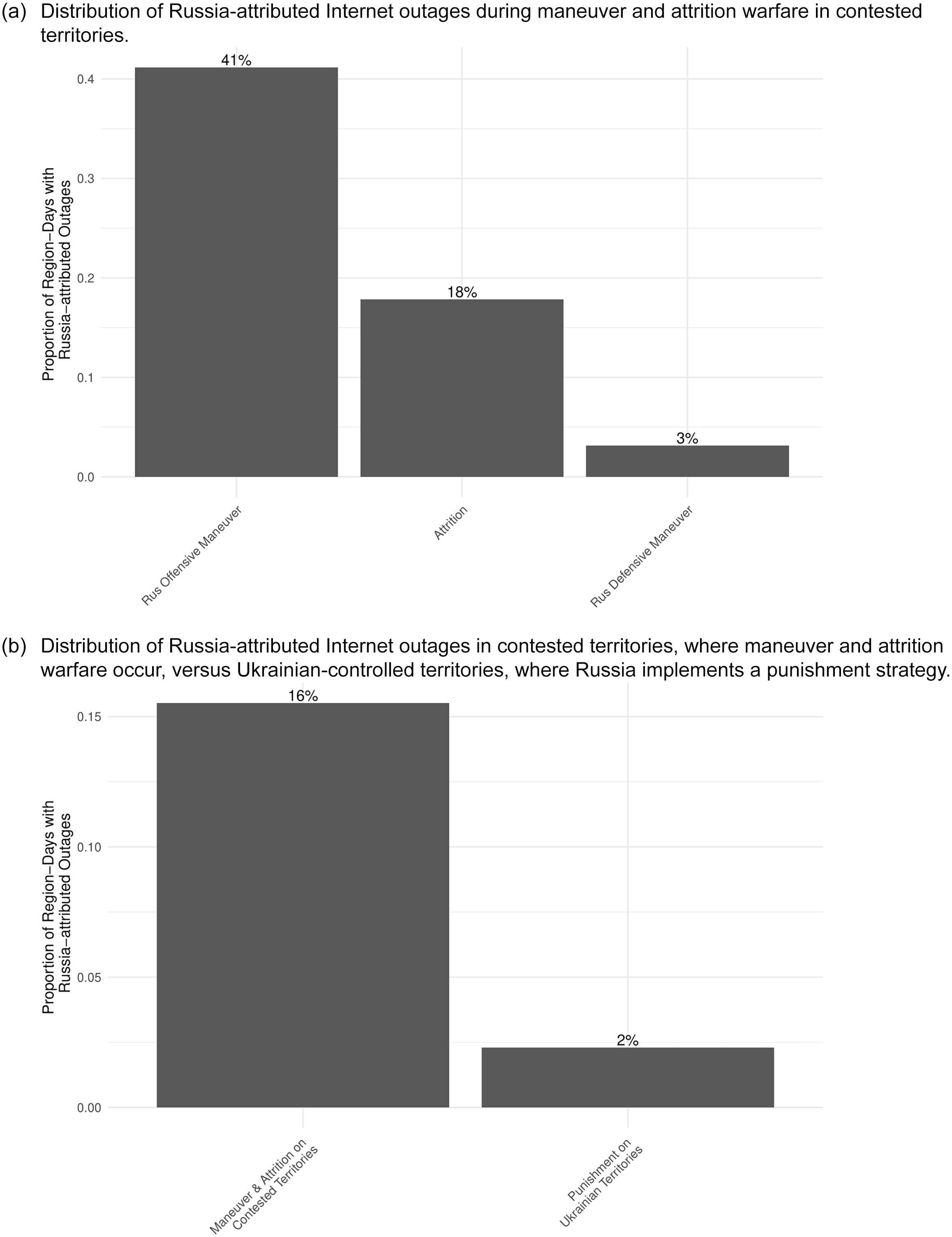
Figure 2, which reports the total number of region-days with Russian-sponsored internet outages, offers a complementary view by showing how often outages occurred relative to the duration of each strategy. Figure 2(a), which focuses on contested territories, indicates that region-days with outages were far more frequent during offensive maneuvers than during attrition, and more common during both offensive maneuvers and attrition than during defensive maneuvers. Figure 2(b) further shows that contested territories – where maneuvers and attrition took place – experienced substantially more region-days with outages than Ukrainian-controlled territories, where Russia employed a punishment strategy.
Proportion of region-days with Russia-attributed internet outages based on different military strategies in its war in Ukraine (2022–3).

Model Choice
Maneuver versus attrition
Using data from contested territories,Footnote 9 we test our hypotheses related to attrition and maneuver strategies by fitting the following generalized linear model:
 $$\eqalign{logit({\rm{Rus}}\;{\rm{Internet}}\;{\rm{Outag}}{{\rm{e}}_{it}},{X_{it}}) = & {{\rm{\beta}} _0} + {{\rm{\beta}} _1}*{\rm{Rus}}\;{\rm{Offensive}}\;{\rm{Maneuve}}{{\rm{r}}_{t - 1}} + {{\rm{\beta}} _2} \\& *{\rm{Rus}}\;{\rm{Defensive}}\;{\rm{Maneuve}}{{\rm{r}}_{t - 1}} + {{\rm{\beta}} _3}*{\rm{Rus}}\;{\rm{Internet}}\;{\rm{Outag}}{{\rm{e}}_{it - 1}} \\& + G{X_{it}} + {\alpha _i} + {\epsilon _{it}},{\alpha _i}{\sim_{iid}}N(0,\sigma _\alpha ^2){\rm{ }}}$$
$$\eqalign{logit({\rm{Rus}}\;{\rm{Internet}}\;{\rm{Outag}}{{\rm{e}}_{it}},{X_{it}}) = & {{\rm{\beta}} _0} + {{\rm{\beta}} _1}*{\rm{Rus}}\;{\rm{Offensive}}\;{\rm{Maneuve}}{{\rm{r}}_{t - 1}} + {{\rm{\beta}} _2} \\& *{\rm{Rus}}\;{\rm{Defensive}}\;{\rm{Maneuve}}{{\rm{r}}_{t - 1}} + {{\rm{\beta}} _3}*{\rm{Rus}}\;{\rm{Internet}}\;{\rm{Outag}}{{\rm{e}}_{it - 1}} \\& + G{X_{it}} + {\alpha _i} + {\epsilon _{it}},{\alpha _i}{\sim_{iid}}N(0,\sigma _\alpha ^2){\rm{ }}}$$
where Rus Internet Outage it is a dummy identifying whether the Russian-sponsored internet outage occurred in region i on day t, and β 0 is an intercept. The primary exposures Rus Offensive Maneuver it − 1 and Rus Defensive Maneuver it − 1 are non-overlapping dummies identifying days during the Russian offensive and defensive maneuver campaigns, respectively, in contested territories on day t − 1, with days where they both are zero representing the base category of Attrition. X it = [x 1it ,…,x nit ]′ is a matrix of n exogenous variables, including a number of the Russian military operations in region i on day t − 1 (Rus Kinetic it − 1),Footnote 10 a dummy variable for Ukrainian, Russian, and Soviet holidays (Holidays), and a dummy variable for a weekend (Weekend).
We control for the number of military operations to account for local variation in combat intensity, which may independently affect the likelihood of internet outages. Because internet disruptions can sometimes complement or support military activity – for example, by undermining co-ordination or communication in targeted areas – this control allows us to better isolate the relationship between broader strategic shifts and other patterns of internet disruption. We use Zhukov (Reference Zhukov2023)’s VIINA as a source for military operations.Footnote 11 We control for holidays and weekends because research indicates a decrease in military activity during these times (Berman et al. Reference Berman, Shapiro and Felter2011). Finally, we add oblast (α i ) random effects. ϵ it is an independent error term.
Punishment
Using data from the Ukrainian-controlled and contested territories,Footnote 12 we test our punishment hypothesis (H2) by fitting the following generalized linear model:
 $$\eqalign{logit({\rm{Rus}}\;{\rm{Internet}}\;{\rm{Outag}}{{\rm{e}}_{it}},{X_{it}}) = & {{\rm{\beta}} _0} + {{\rm{\beta}} _1}*{\rm{Rus}}\;{\rm{Punishment}}\;{\rm{in}}\;{\rm{Ukr}}\;{\rm{Territorie}}{{\rm{s}}_{t - 1}} + {{\rm{\beta}} _2} \\& *{\rm{Rus}}\;{\rm{Internet}}\;{\rm{Outag}}{{\rm{e}}_{it - 1}} + G{X_{it}} + {\alpha _i} + {\epsilon_{it}},{\alpha _i}{\sim_{iid}}N(0,\sigma _\alpha ^2)}$$
$$\eqalign{logit({\rm{Rus}}\;{\rm{Internet}}\;{\rm{Outag}}{{\rm{e}}_{it}},{X_{it}}) = & {{\rm{\beta}} _0} + {{\rm{\beta}} _1}*{\rm{Rus}}\;{\rm{Punishment}}\;{\rm{in}}\;{\rm{Ukr}}\;{\rm{Territorie}}{{\rm{s}}_{t - 1}} + {{\rm{\beta}} _2} \\& *{\rm{Rus}}\;{\rm{Internet}}\;{\rm{Outag}}{{\rm{e}}_{it - 1}} + G{X_{it}} + {\alpha _i} + {\epsilon_{it}},{\alpha _i}{\sim_{iid}}N(0,\sigma _\alpha ^2)}$$
where Rus Internet Outage it is a dummy identifying whether the Russian-sponsored internet outage occurred in region i on day t, and β 0 is an intercept. The primary exposure Rus Punishment in Ukr Territories it − 1 is a dummy identifying whether region i was under Ukrainian or contested control on day t − 1. Therefore, β 1 represents the difference on the log-odds scale in Russian-attributed outages between the Ukrainian-controlled territories, where outages are interpreted as punishment, versus contested territories, where they are used during combat. All other terms are the same as defined in Equation (1).
Findings: Russia’s Use of Internet Outages in Ukraine War
This section presents the results from the quantitative analysis of Russian use of internet outages in the war in Ukraine (see Table 2). The analysis of Ukrainian actions appears in Online Appendix Section 3. Evidence from both sides confirms that actors strategically employ internet disruptions more frequently during their offensive maneuver campaigns than during attrition or defensive maneuver combat, all of which take place in contested territories. Moreover, internet outages tend to occur at a higher rate in contested territories than in enemy-controlled territories, where actors practice punishment.
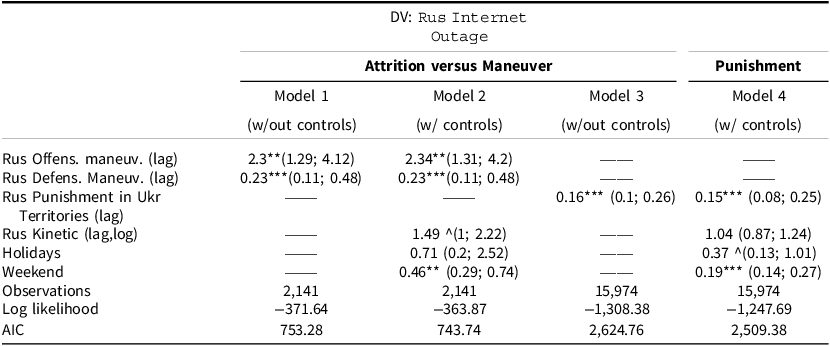
Russia’s use of internet outages in its war in Ukraine (odds ratios and confidence intervals)

Note: this table examines the use of internet outages by the Russian military and/or government during different warfare strategies in its war in Ukraine. The reported values are the odds ratios and confidence intervals. Odds ratios larger than 1 identify positive correlation, and those smaller than 1 identify negative correlation. All models contain an intercept, a lag of a dependent variable, and region-random effects. The Online Appendix contains complete results. Internet disruptions occur at a higher rate during offensive maneuver combat than during attrition combat or defensive maneuvers. Internet outages are less likely to be used as a form of punishment on the Ukrainian-controlled territories than along the front line on contested territories. ∧ p < 0.1; *p < 0.05; **p < 0.01; * * * p < 0.001.
Main Results
Table 2 presents the obtained results. The reported values in this table are the odds ratios and confidence intervals. Odds ratios larger than 1 identify positive correlation, and those smaller than 1 identify negative correlation.
Model 1 demonstrates how Russia’s use of internet outages varies across different types of combat. The findings indicate that during Russian offensive maneuver campaigns, the odds of experiencing a Russian-sponsored internet outage are 130 per cent higher than during attrition warfare, which serves as the base category in this model. In contrast, during Russian defensive maneuver campaigns, the odds of experiencing a Russian-sponsored internet outage are 77 per cent lower than during attrition warfare. These results hold when we account for additional controls in Model 2. For example, there is a 4.44 per cent chance of a Russia-sponsored outage occurring during the Russian offensive maneuver campaign where the other variables are at the reference value of zero. In comparison, the likelihood of an outage during attrition warfare is just 1.95 per cent. During defensive maneuver campaigns, this likelihood drops even further, to only 0.45 per cent.
Together, these results support H1A–H1C, confirming that the Kremlin strategically employs internet disruptions more frequently during its offensive maneuver campaigns than during its attrition or defensive maneuver campaigns. For example, during the 2022 invasion of Ukraine, Russia strategically used internet outages in its offensive campaigns to disrupt Ukrainian communications, especially in contested regions like Kharkiv and Donetsk, where such disruptions were crucial for military maneuvering. In contrast, during defensive maneuvers, such as in regions like Luhansk, the use of internet outages was less frequent, as the focus shifted to defending occupied territory rather than disrupting enemy communications.
Models 3 and 4 compare Russia’s use of internet outages as part of its punishment strategy on the Ukrainian-controlled territories versus its use during maneuver and attrition warfare on contested territories. Model 4 demonstrates that the odds of experiencing a Russian-sponsored internet outage are 85 per cent lower in Ukrainian-controlled territories than in contested territories. For example, there is a 6.8 per cent chance of a Russia-sponsored outage occurring in a contested territory where the other variables are at the reference value of zero. In comparison, the likelihood of an outage on the Ukrainian-controlled territories is just 1 per cent. These results support our hypothesis (H2) that internet disruption is less likely in punishment contexts, where combatants operate under tighter constraints and instead focus on institutional exploitation.
Models in Table 2 also reveal several interesting relationships between our dependent variable and the control variables. Model 2 shows a positive, marginally significant association between Russian military operations and internet outages, indicating that such operations may be linked to increased outage likelihood during maneuver and attrition campaigns. The odds of experiencing a Russia-attributed internet outage are lower on weekends compared to weekdays (for example, OR: 0.19; CI: (0.14; 0.27) in Model 4).
Robustness Checks and Alternative Explanations
We conducted a number of robustness checks to further confirm the plausibility of our theory, including (1) the alternative measure of territorial control (at least 70 per cent as opposed to 80 per cent); (2) the alternative model specification (probit, fixed effects); (3) the alternative measure of military strategy, which accounts for regional variations within a single war phase; (4) a sensitivity analysis assessing the potential misclassification of outage intentionality; and (5) a model estimated without the lagged dependent variable, treating all days of outage as potentially strategic. Our results remain robust to these tests (see Online Appendix Section 2.3).
Another potential concern is endogeneity, particularly the possibility of reverse causality between institutional disruption and strategic phases. To reduce these concerns, we lag our independent variables – a common approach in related work (see, for example, Choi (Reference Choi2022)) – and include region fixed effects as well as controls for temporal variation in conflict intensity. We further assessed the sensitivity of our findings to unmeasured confounding using an E-value analysis (Haneuse et al. Reference Haneuse, VanderWeele and Arterburn2019). The E-value represents the minimum strength of association an unobserved confounder would need to have with both the exposure and the outcome to fully explain away the effect. In our case, the E-value is substantially high (see Online Appendix Section 2.3.6), suggesting that unmeasured confounding would need to be very strong to overturn our conclusions. While we remain cautious in making causal claims, the combined evidence suggests that the observed patterns are consistent with our theoretical expectations.
Here, we also consider several alternative explanations relevant to Russia’s actions. The first focuses on Russia’s significant cyber capabilities, addressing the disparity between an actor’s actual and perceived capacity for cyber exploitation. Some might argue that Russia’s belief in its cyber prowess for exploitation could explain its reluctance to completely shut down the internet in Ukraine or to engage in cyber disruption tactics. A state that perceived itself as less capable in cyber exploitation might focus more on disruption. This explanation, however, raises a question: If Russia’s actions were based on its reputation as one of the most capable actors in cyber exploitation, why would it resort to internet outages at all? Moreover, the outages are not random; they exhibit clear territorial and temporal patterns, further undermining this alternative explanation. In fact, Russia’s strong capabilities in cyber exploitation make this an even harder case to test our theory, as it represents the least likely scenario for internet disruptions. Therefore, the support we found for our theory in this unlikely context only underscores the robustness and relevance of our explanations. It also reinforces our central claim that variation in institutional disruption stems not only from cyber capacity, but from the strategic and spatial conditions under which warfare is conducted.
Another alternative explanation – treating the internet as infrastructure rather than as an institution – posits that Russia’s primary goal is to deprive Ukrainians of public goods and disrupt critical infrastructure, making internet outages a secondary, unintended consequence. If this infrastructure-disruption mechanism were correct, Russian military activity should be positively associated with internet outages. The results in Model 2 (Table 2) show a positive but marginally statistically significant relationship between Russian military operations and outages during maneuver and attrition campaigns, suggesting at most a weak association. To probe this further, we estimated an additional model controlling specifically for Russian airstrikes – operations frequently used to target infrastructure. As shown in Online Appendix Section 2.4.1, these results align with our main findings: outages do not appear to be merely a secondary effect of infrastructure attacks. Moreover, Model 4 (Table 2) indicates that Russian military activity is unlikely to drive outages in Ukrainian-controlled areas (OR: 1.04; CI: 0.87–1.24), and this pattern also holds when focusing solely on airstrikes (Online Appendix Section 2.4.1). Together, these results suggest that Russian internet outages are not simply byproducts of broader destructive operations but are more consistent with a deliberate strategic choice.
We acknowledge that these results do not preclude the possibility that isolated, high-impact strikes on critical infrastructure – such as power substations or telecommunications nodes – may, in some instances, lead to significant disruptions. A single, strategically targeted strike could produce a substantial outage without generating a detectable pattern across the broader dataset. Importantly, the potential for such isolated incidents does not contradict our interpretation; rather, it supports it. The use of precision strikes against internet infrastructure reflects strategic intent, aligning with our argument that many internet disruptions are the result of deliberate targeting rather than incidental damage. Thus, while rare outlier events may occur, the absence of a consistent statistical relationship reinforces the conclusion that outages are not primarily unintended consequences of kinetic operations, but often intentional and systematic.
Another possible explanation concerns Ukraine’s internet resilience, which can be attributed to substantial Western support throughout the war. This resilience may influence the number of outages caused by Russia’s cyber operations, as the data captures only successful attempts and does not account for failed attacks. Given the significant boost to Ukraine’s cyber defenses from Western support, we might expect to see a decline in the number of outages caused by cyber operations over time. However, descriptive data, presented in Online Appendix Section 2.4.2, show that this is not the case by demonstrating a higher number of internet outages in winter 2023 – almost two years into the conflict – compared to earlier phases of the war. Furthermore, even if the increase in resilience were to work, and we observed, as the war progressed, a decreasing number of Russia-sponsored internet outages resulting from cyber operations, this would introduce a possible attenuation bias, indicating that our data likely represented the lower bound of true outages. As a result, we could conclude that the true coefficients were higher and that our findings underestimated the actual effect size of internet outages, making our claims more conservative. This would suggest that the relationship between combat dynamics and internet outages may be stronger than this article reports, further reinforcing our theory.
Evidence Beyond Ukraine
Evidence on internet shutdowns in Azerbaijan, Armenia, India, Israel, Lebanon, Pakistan, and Yemen reveal that internet connectivity has been a target of both military and cyber campaigns during active conflicts in these nations (Access Now 2021,2024), suggesting that the lessons we glean about connectivity and combat from the Ukraine war could have broader relevance. To further demonstrate this, Online Appendix Section 4 briefly discusses the 2020 and 2023 Armenia–Azerbaijan conflicts over the Nagorno-Karabakh region. The evidence from both conflicts offers strong support for our theory, illustrating the applicability of our findings to other international disputes.
Discussion
This article has shown that combatants’ decisions to maintain or disrupt collective institutions during war are not uniform or structurally determined, but, instead, vary predictably with battlefield dynamics. Specifically, we find that the degree of operational constraint – related to military strategy (maneuver, attrition, or punishment) – plays a central role in determining when and where combatants are willing to sacrifice or preserve collective institutions. These findings deepen our understanding of how institutional interdependence is tactically managed during conflict, shifting the conversation from questions of war onset and termination to those of wartime conduct.
Using the internet as a representative case of a collective institution, we show that combatants are more likely to disrupt connectivity when engaged in offensive maneuver operations, where a high degree of control and initiative provides opportunities for battlefield momentum and incentivizes prioritizing surprise. Conversely, combatants facing greater constraints – such as defenders in maneuver warfare – are more inclined to preserve internet connectivity, as they depend more heavily on co-ordination and communication. Attrition strategies, with their more stable and reciprocal constraints, tend to produce selective disruptions, balancing the costs and benefits of connectivity. Our spatial analysis further reveals that internet disruptions are concentrated in contested zones and are relatively rare in enemy-held areas, where punishment strategies dominate and institutional preservation may better serve indirect-influence goals.
Our approach is not without limitations, which offer opportunities for future work. Our theory assumes symmetric interdependence, where both sides rely similarly on shared institutional networks. In wartime, however, asymmetric interdependence can emerge when actors insulate themselves from shared networks, gaining strategic advantages while altering mutual vulnerability. For example, Ukraine’s use of Starlink enhanced resilience by protecting military communications from Russian attacks on terrestrial infrastructure. Such measures also affect responsiveness, as secure communications enable more co-ordinated and timely actions. Investigating how asymmetric interdependence is exploited in war – and how actors navigate trade-offs between resilience and responsiveness – represents a promising avenue for future research, complementing what we already know from peacetime contexts (Farrell and Newman Reference Farrell and Newman2019).
Our analysis makes two main contributions, one methodological and one substantive. Methodologically, we demonstrate the potential of multidisciplinary collaboration. The internet measurement community has developed sophisticated techniques for monitoring and characterizing large-scale information systems – including traffic patterns, outages, and protocol usage – that hold tremendous untapped potential for political science research. These data can be used as both dependent and independent variables and serve as proxies for economic interdependence and other political phenomena. In addition, our improved quantitative measure of the military strategies that combatants employ simultaneously across different localities enables near-real-time analysis of battlefield dynamics, providing a deeper understanding of how strategy shapes combatant decision making as it unfolds. While this measure captures broad, theater-level shifts in strategy, localized variations may also be important. Limited data granularity and uncertainty about the intent behind individual actions currently constrain systematic identification of such patterns, but future access to more detailed operational records – particularly through archival releases – will allow researchers to better assess how micro-level battlefield decisions align with broader strategic objectives.
Our substantive contribution is a new theory of institutional targeting in war. Rather than treating collective institutions as either casualties of war or safeguards of peace, we argue that they are operational resources during conflict – tools to be preserved or disrupted depending on strategic objectives.
Although our empirical focus is on the internet, our framework may extend to other wartime institutions. For example, in maneuver warfare, combatants may sever supply chains, block humanitarian aid, or disrupt trade to exploit their advantage. In contrast, during stalemates or in enemy-held areas, combatants may deliberately maintain those same institutions, both for strategic gain and to avoid backlash. Historical cases from World War I illustrate this logic. During the war’s attritional phases, both sides tolerated and regulated neutral trade and humanitarian relif systems such as the Commission for Relief in Belgium, which delivered food to civilians in German-occupied territories. By contrast, large-scale offensives–such as Germany’s 1918 Spring Offensive--disrupted civilian administration and logistical networks in newly captured areas, interrupting existing relief and supply systems.
Our findings also speak to broader theories of institutional resilience. Even under the extreme conditions of war, shared institutions can persist – not merely as remnants of peacetime order, but as adaptable instruments shaped by strategic incentives. This supports theories that view institutions not just as constraints, but as political resources with which actors selectively engage (Coase Reference Coase1981; Cox and McCubbins Reference Cox and McCubbins2005). The propensity of combatants to preserve institutions under certain conditions illustrates how institutional ‘stickiness’ operates not just in politics and economics, but also in armed conflict.
In conclusion, this study identifies a critical yet overlooked hinge point in international relations: the management of interdependence during war. Rather than collapsing under violence, institutions can be retooled and redeployed in service of war aims, with their fate contingent on shifting strategic demands of wartime operations. It also opens new avenues for IR research by highlighting the tactical, localized, and strategic logics that govern institutional use under extreme conditions.
Crucially, our findings have implications for post-war peace building and the reconstruction of institutions. When institutions are preserved or deliberately instrumentalized during war, they do not emerge from conflict as neutral remnants of a previous system but as shaped tools – either degraded or embedded in wartime power structures. Understanding this legacy is vital for designing post-conflict institutions that support genuine recovery rather than reinforce divisions. How institutions are used in war, in other words, helps determine the kind of peace that follows.
Supplementary material
The supplementary material for this article can be found at https://doi.org/10.1017/S0007123426101379.
Data availability statement
Replication data and code can be found in Harvard Dataverse: https://doi.org/10.7910/DVN/W00BC2
Acknowledgments
We would like to thank Michael Colaresi, Andres Gannon, Erik Gartzke, Ryan Grauer, Harry Oppenheimer, Burcu Savun, Ryan Shandler, Brandon Valeriano, and the participants of the cyber conflict pre-conference workshop held at the 2023 American Political Science Association meeting, the Political Science Research Workshop at the Carnegie Mellon Institute for Strategy and Technology, and the Global Politics Seminar at the University of Pittsburgh.
Funding statement
This research received no specific grant from any funding agency, commercial or not-for-profit sectors.
Competing interests
None.