Refine search
Actions for selected content:
52651 results in Statistics and Probability
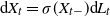
Predicting the last zero before an exponential time of a spectrally negative Lévy process
- Part of
-
- Journal:
- Advances in Applied Probability / Volume 55 / Issue 2 / June 2023
- Published online by Cambridge University Press:
- 16 January 2023, pp. 611-642
- Print publication:
- June 2023
-
- Article
- Export citation
Response to COVID-19 in Lebanon: update, challenges and lessons learned
-
- Journal:
- Epidemiology & Infection / Volume 151 / 2023
- Published online by Cambridge University Press:
- 16 January 2023, e23
-
- Article
-
- You have access
- Open access
- HTML
- Export citation
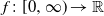
Transition density of an infinite-dimensional diffusion with the jack parameter
- Part of
-
- Journal:
- Journal of Applied Probability / Volume 60 / Issue 3 / September 2023
- Published online by Cambridge University Press:
- 16 January 2023, pp. 797-811
- Print publication:
- September 2023
-
- Article
- Export citation
Index
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp 137-138
-
- Chapter
- Export citation
Glossary
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp 131-131
-
- Chapter
- Export citation
Preface
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp xi-xii
-
- Chapter
- Export citation
4 - Averaging
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp 41-58
-
- Chapter
- Export citation
5 - Covers and Embeddings
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp 59-76
-
- Chapter
- Export citation
3 - Applications
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp 20-40
-
- Chapter
- Export citation
References
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp 132-136
-
- Chapter
- Export citation
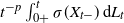
Short-time behavior of solutions to Lévy-driven stochastic differential equations
- Part of
-
- Journal:
- Journal of Applied Probability / Volume 60 / Issue 3 / September 2023
- Published online by Cambridge University Press:
- 12 January 2023, pp. 765-780
- Print publication:
- September 2023
-
- Article
- Export citation
Invariant Galton–Watson trees: metric properties and attraction with respect to generalized dynamical pruning
- Part of
-
- Journal:
- Advances in Applied Probability / Volume 55 / Issue 2 / June 2023
- Published online by Cambridge University Press:
- 12 January 2023, pp. 643-671
- Print publication:
- June 2023
-
- Article
- Export citation
7 - Shunts
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp 98-120
-
- Chapter
- Export citation
8 - 1-Dimensional Walks
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp 121-130
-
- Chapter
- Export citation
1 - Grover Search
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp 1-10
-
- Chapter
-
- You have access
- Export citation
6 - Vertex-Face Walks
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp 77-97
-
- Chapter
- Export citation
Contents
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp vii-x
-
- Chapter
- Export citation
Frontmatter
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp i-vi
-
- Chapter
- Export citation
2 - Two Reflections
-
- Book:
- Discrete Quantum Walks on Graphs and Digraphs
- Published online:
- 23 December 2022
- Print publication:
- 12 January 2023, pp 11-19
-
- Chapter
- Export citation
From text to ties: Extraction of corruption network data from deferred prosecution agreements
-
- Journal:
- Data & Policy / Volume 5 / 2023
- Published online by Cambridge University Press:
- 11 January 2023, e4
-
- Article
-
- You have access
- Open access
- HTML
- Export citation